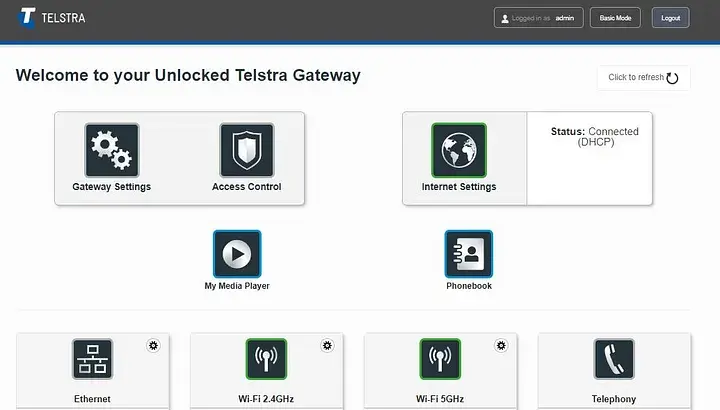
Sorry Telstra but this is my F@ST 5355 router
I decided to give Pi-hole a go, having endured yet another ad-laden website.
All went well — installation was smooth and it was up and running 15 minutes later.
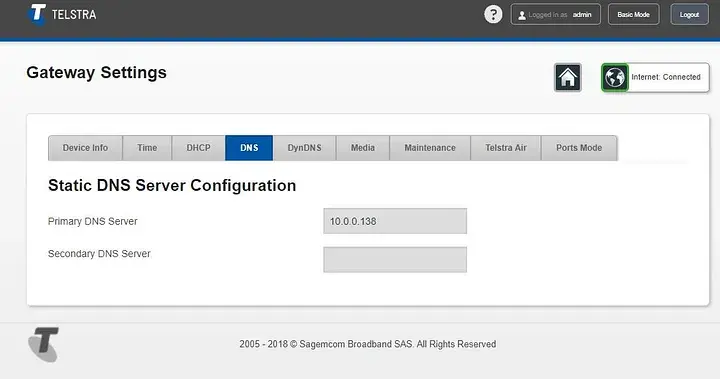
All that remained was to set my router’s DNS server to the Pi’s and my home devices would be safe.
I remember seeing the option in there for it.
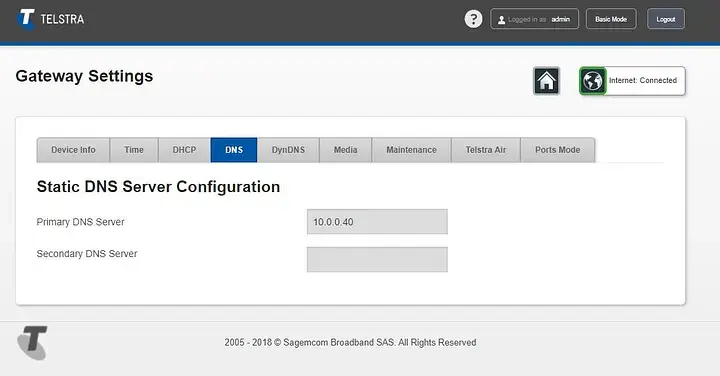
WTF?
It was now disabled. A quick Google around revealed that about a year ago (June 2017) Telstra simply decided to remove that functionality.
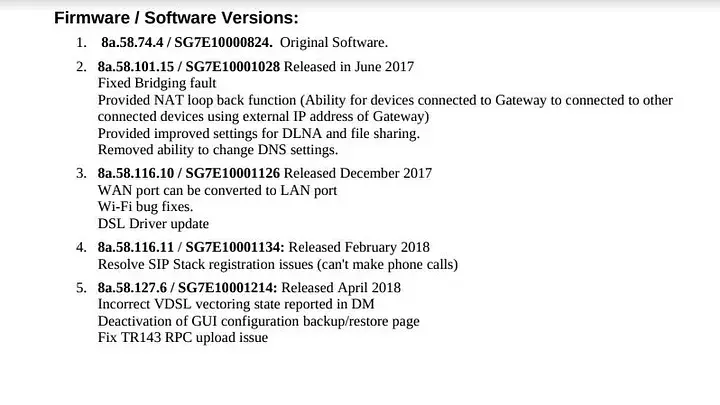
Cool, less features as time goes on.
Surely it had nothing to do with the Australian government implementing DNS-based censorship in June 2017?
So fuck you, Telstra — that’s my router you made me purchase.
Time to find out how to take it back.
I found some incredible hacking work done previously at noconroy.net — however that used the device’s Backup/Restore functionality, which was recently removed by our Telstra overlords via another firmware update. Issued not long after his work was posted. Just more coincidences it seems.
Another site with lots of great info was tripleoxygen.net.
They had found that the web UI’s framework allowed directly logging in as the internal admin (not you, the owner), appearing to skip some of the checks and essentially gaining root access.
And once again, those tricks had been disabled via a firmware update.
While the functions could still be called to make config changes, most of the built-in accounts lacked remote access settings, and trying to update config for almost anything but your own user resulted in the router logging you out to start again.
$.xmo.getValuesTree("Device");
Still returned a 1 MB JSON config object full of interesting stuff including 8 other accounts and their poorly hashed passwords, plenty of username/password/url’s for Telstra services, and lots of other config settings to try and change.
However, what was allowed and what wasn’t seemed a little hit or miss.
For example, I could re-enable the daily backup functionality but the path for the backups seemed to be locked. I could re-enable FTP but not SFTP — it all seemed a little half-arsed.
Finally I found the account assist had remote access settings that were disabled.
Trying to alter the remote access settings for the other accounts resulted in the logout thing, but this one didn’t — and it had an SSH entry! To get to the point:
// Enable remote access
$.xmo.setValuesTree(true, "Device/UserAccounts/Users/User[@uid='6']/RemoteAccesses/RemoteAccess[@uid='2']/Enabled");
// Give it a port
$.xmo.setValuesTree(22, "Device/UserAccounts/Users/User[@uid='6']/RemoteAccesses/RemoteAccess[@uid='2']/Port");
// Allow LAN login
$.xmo.setValuesTree("ACCESS_ENABLE_ALL", "Device/UserAccounts/Users/User[@uid='6']/RemoteAccesses/RemoteAccess[@uid='2']/LANRestriction");
// Give the 'assist' account a password (MD5 of 'assist')
$.xmo.setValuesTree("8213d162ea32a3fcfec2aae5538c48e5", "Device/UserAccounts/Users/User[@uid='6']/Password");
// Set the SSH password
$.xmo.setValuesTree("assist", "Device/UserAccounts/Users/User[@uid='6']/ClearTextPassword");
Reboot, and when it comes back up you’ll have an SSH server waiting on port 22.
Login with assist:assist. Once in, run su and the password is root.
And bingo — you have control of your router again.
I’m still making sense of what’s here as there’s a lot to go through — your SIP settings (so you can plug them into another device for your home phone) are there and lots more Telstra API user/passwords that I’m yet to look into.
However, to get started, almost the same XMO interface is available via CLI, and as root you won’t have any trouble making changes. I did a few things like:
# Change the port Telstra’s update app listens on
xmo-client -s 50806 -p "Device/ManagementServer/TR69InternalData/Settings/Port"
# Turn off the CWMP check-in with Telstra’s servers
xmo-client -s false -p "Device/ManagementServer/EnableCWMP"
# Turn off the Telstra AIR Wi-Fi that lets others use your connection
xmo-client -s false -p "Device/WiFi/SSIDs/SSID[@uid='5']/Enable"
xmo-client -s false -p "Device/WiFi/SSIDs/SSID[@uid='7']/Enable"
# Finally, change DNS to Pi-hole
xmo-client -s "10.0.0.40" -p "Device/DHCPv4/Server/Pools/Pool[@uid='1']/DNSServers"
And enjoy sweet, sweet (mostly) ad-free internet — safe in the knowledge my router is mine again.
Hilarious.